In the world of technology, ensuring the security and authenticity of user identities is paramount. Biometric authentication technologies provide a reliable way to verify user identities using biometric data instead of a traditional username. Biometric authentication technologies provide a reliable way to verify user identities using biometric data instead of a traditional username. Biometric authentication technologies provide a reliable way to verify user identities using biometric data instead of a traditional username. This is where face liveness verification comes into play. By combining liveness detection, identity verification, and biometric authentication technologies, this advanced device adds an extra layer of protection to various applications and systems through face matching. This hybrid technology is highly secure and efficient.
Liveness detection is a crucial part of biometric authentication and face liveness verification, as it helps distinguish between real individuals and deepfake spoofing attempts. This authentication technology relies on analyzing biometric data to ensure the authenticity of the user. Techniques like eye blinking or head movement analysis are used for liveness checking to ensure that the person being verified is physically present during biometric authentication. These liveness checks rely on the face liveness feature. Identity verification uses authentication technology to confirm the identity of an individual by analyzing their facial biometrics. This process helps prevent impersonation or fraud by incorporating deepfake detection and liveness checking. Face liveness verification enhances the security and reliability of biometric authentication systems by allowing consumers to use only live individuals to access sensitive information or perform transactions.
Understanding Liveness Detection
In the world of technology, ensuring the security and authenticity of user identities is paramount. Biometric authentication technologies provide a reliable way to verify user identities using biometric data instead of a traditional username. It is a key component of biometric authentication, ensuring the use of biometric data to authenticate consumers. It is a key component of biometric authentication, ensuring the use of biometric data to authenticate consumers. By utilizing advanced algorithms and AI technology, this process analyzes various facial cues to determine the authenticity of biometric data and ensure liveness detection for consumers using biometric authentication.
The basic principles of face liveness verification involve analyzing factors such as motion, depth perception, multi-modality, and biometric authentication using biometric data. In the world of technology, ensuring the security and authenticity of user identities is paramount. Biometric authentication technologies provide a reliable way to verify user identities using biometric data instead of a traditional username. This technology is particularly useful for capturing and analyzing biometric data. This technology is particularly useful for capturing and analyzing biometric data. Depth perception allows the system to differentiate between a real face with three-dimensional features and a two-dimensional photo or video, ensuring accurate liveness detection of biometric data. Multi-modality refers to the use of multiple sensors, such as infrared or 3D cameras, to capture additional information about the face, including biometric data and enabling liveness detection.
Verification, including liveness detection, plays a vital role in preventing unauthorized access, fraud, and identity theft. With the increasing reliance on digital platforms for various services like banking and e-commerce, ensuring the accuracy and reliability of identity verification, including liveness detection, becomes paramount. Face liveness verification adds an extra layer of security by confirming that the person attempting access is physically present and not using fraudulent means.
By implementing face liveness verification, organizations can build trust among their users. When individuals see robust liveness detection security measures in place during the authentication process, they are more likely to feel confident about sharing sensitive information or conducting transactions online. This reduces the risk of fraudulent activities and enhances overall user experience with liveness detection.
AI algorithms play a key role in face liveness verification by analyzing facial features and movements. These algorithms are trained to detect anomalies that may indicate spoofing attempts or fake representations using liveness detection. By continuously learning from large datasets containing both genuine and fraudulent examples, AI models incorporating liveness detection become increasingly accurate over time.
Continuous advancements in AI technology contribute to improving the effectiveness of face liveness verification systems. As researchers develop more sophisticated algorithms capable of detecting even subtle signs of deception or manipulation, these systems, equipped with liveness detection, become more resilient against emerging threats.
Face Liveness Verification Explained
Face liveness verification is a crucial aspect of modern security systems that aims to ensure the authenticity and liveliness of a user’s face. By differentiating between real faces and fake ones, liveness detection technology helps prevent unauthorized access and fraudulent activities.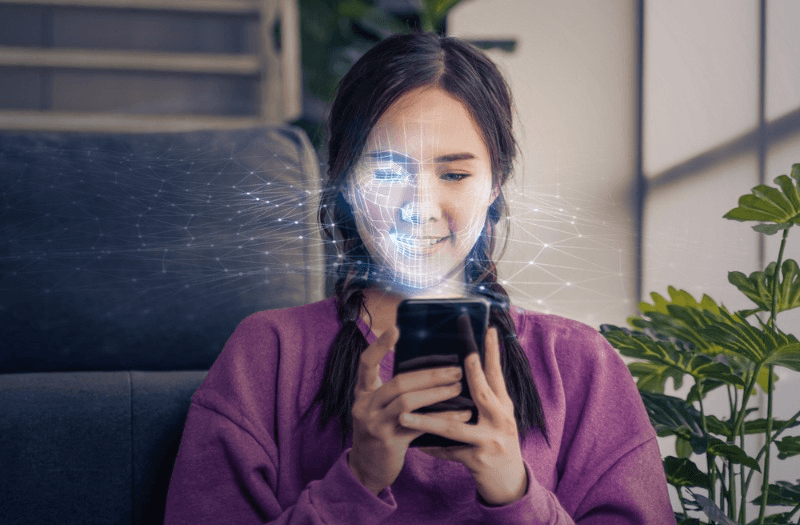
Active Detection
Active detection plays a vital role in face liveness verification. Liveness detection involves the use of stimuli or challenges to prompt a response from the user during the verification process, ensuring the authenticity and liveliness of the individual. By requesting specific facial movements or responses to random prompts, active detection ensures that the individual being verified is physically present and actively participating.
For example, during the verification process, a liveness detection system might ask users to smile, blink their eyes, or turn their head slightly. These actions help validate the liveness detection, ensuring that it is indeed a live person in front of the camera rather than an impersonator or an image/video representation.
Active detection adds an extra layer of security by requiring real-time physical interaction with the system. This reduces the risk of spoofing attempts where static images or pre-recorded videos are used to deceive facial recognition systems by implementing liveness detection.
Passive Detection
In contrast to active detection, passive detection relies on analyzing facial cues and characteristics without requiring any specific user response. Advanced AI algorithms are employed to detect signs of liveness based on natural facial movements such as eye blinking or subtle changes in expression.
By monitoring these micro-expressions and other dynamic features, passive detection can accurately determine whether a face is live or not. This approach enhances user experience by eliminating the need for explicit user actions during verification, thanks to the implementation of liveness detection. This ensures high levels of security.
Passive detection has become increasingly popular due to its convenience and seamless integration into various applications. Liveness detection allows for faster and more intuitive authentication processes without compromising security standards.
Challenge-Response Role
The challenge-response role is another important aspect of face liveness verification. It involves presenting users with specific tasks or prompts to prove their liveness. Users are required to respond appropriately, following instructions or making specific facial movements as requested for liveness detection.
For instance, a system might ask users to nod their head in response to a prompt or follow a sequence of facial gestures to ensure liveness detection. By actively engaging the user in these challenges, the verification process ensures that an actual person is present and actively participating.
The challenge-response role serves as a deterrent against spoofing attempts by impostors who may try to deceive the system using static images or pre-recorded videos. It adds an additional layer of security by requiring real-time interaction and responsiveness from the user.
Methods of Liveness Detection
Liveness detection is a crucial aspect of face verification systems, ensuring that the person being authenticated is physically present and not using a fraudulent representation. To achieve accurate results, various methods are employed to detect liveness. Let’s explore three key methods: depth perception, motion analysis, and multi-modality.
Depth Perception
Depth perception plays a vital role in face liveness verification by analyzing the three-dimensional aspects of a face. This technique helps differentiate between real faces and flat images or masks used in spoofing attempts. By capturing depth information, such as variations in facial contours and surface texture, the system can determine the authenticity of the presented face.
Imagine trying to distinguish between a photograph of a person’s face and an actual living person standing in front of you. The ability to perceive depth allows you to identify subtle differences that indicate whether it is a real human or just an image. Similarly, depth perception algorithms analyze facial geometry and texture patterns to identify signs of liveness.
Motion Analysis
Motion analysis is another significant method employed in detecting liveness during face verification. Algorithms examine various facial movements, such as blinking, smiling, or head rotations, to confirm the presence of a live person. By analyzing these dynamic features, the system can verify that the individual is actively participating in the authentication process.
Consider how our own intuition works when we interact with others in-person. We naturally observe their facial expressions and movements while engaging in conversation or any other activity. Similarly, motion analysis algorithms mimic this intuitive observation by examining specific actions that are difficult for fraudsters to replicate accurately.
Accurate motion analysis contributes to reliable face liveness verification results since it focuses on genuine physiological responses unique to live individuals. By incorporating these dynamic cues into the authentication process, potential attackers using static images or videos can be effectively thwarted.
Multi-Modality
Multi-modality refers to utilizing multiple biometric factors for enhanced security and accuracy in face liveness verification. By combining face recognition with other biometric modalities like fingerprint or voice recognition, the authentication process becomes more robust and resistant to spoofing attempts.
Imagine a scenario where an individual tries to bypass face verification by using a high-quality mask that successfully deceives the system. However, if the system also requires fingerprint or voice authentication simultaneously, it becomes significantly harder for the fraudster to bypass all these different modalities.
Multi-modality increases the difficulty for fraudsters attempting to impersonate another person since they would need to replicate multiple biometric factors accurately. This approach strengthens the overall security of face liveness verification systems by adding layers of protection.
Enhancing Security with Liveness Detection
Face liveness verification plays a crucial role in enhancing security measures by adding an extra layer of protection against various threats. Let’s explore some of the key benefits and challenges associated with face liveness verification.
Bot Detection
One of the significant advantages of face liveness verification is its ability to detect and prevent bot activities or automated spoofing attempts. Bots often lack the capability to accurately mimic human facial movements, making them distinguishable from live individuals. By incorporating face liveness verification into systems, organizations can effectively identify and block bot-based attacks.
For instance, imagine a scenario where an online platform requires users to verify their identity before accessing certain features or services. Without proper liveness detection, bots could easily bypass this security measure by using pre-recorded videos or images. However, with face liveness verification in place, these fraudulent attempts can be identified and thwarted, ensuring that only genuine users gain access.
Deepfake Challenges
While face liveness detection is effective against many types of attacks, it faces challenges when dealing with deepfakes. Deepfake technology has advanced significantly in recent years, enabling the creation of highly realistic fake videos or images that mimic real faces. These manipulated media can deceive traditional face recognition systems.
To counter the threat posed by deepfakes, advanced algorithms and continuous research are necessary. Researchers are constantly developing innovative techniques to differentiate between genuine faces and deepfake-generated content. These advancements help improve the accuracy and reliability of face liveness verification systems.
Presentation Attack Types
Presentation attacks encompass various techniques used to deceive face liveness verification systems. Some common examples include using printed photos, masks, or video replays to impersonate a live person. Face liveness verification aims to detect and prevent such presentation attacks by analyzing additional factors beyond static facial features.
User Experience and Liveness Verification
In today’s digital world, where online fraud and identity theft are prevalent, organizations need robust security measures to protect their users’ accounts and sensitive information. One such measure is face liveness verification, which not only enhances security but also improves the overall user experience.
Onboarding Processes
Face liveness verification plays a crucial role in onboarding processes for new users. It ensures that only genuine individuals can create accounts or access services. By verifying both identity and liveness during onboarding, organizations can establish a trusted user base.
Imagine signing up for a new online banking account. During the registration process, you are asked to take a selfie or record a video to verify your identity. The system then uses facial recognition technology to analyze your facial features and movements, ensuring that you are physically present and not using a static image or pre-recorded video.
This added layer of security helps prevent fraudulent account creation by bots or unauthorized individuals attempting to impersonate someone else. It instills confidence in users that their personal information is safeguarded, leading to increased trust in the platform.
Step-Up Authentication
Step-up authentication involves additional security measures beyond the initial login or verification process. Face liveness verification can be used as a step-up authentication method for high-risk transactions or when accessing sensitive data.
For example, let’s say you want to transfer a large sum of money from your bank account. In addition to entering your password or providing other credentials, the system may prompt you to perform face liveness verification as an extra layer of protection. This ensures that even if someone gains unauthorized access to your credentials, they cannot complete the transaction without physically being present.
By implementing face liveness verification as part of step-up authentication, organizations can mitigate risks associated with fraudulent activities such as account takeovers or unauthorized access attempts. It provides an additional barrier against potential threats while maintaining a seamless user experience.
Age Verification
Face liveness verification can also be utilized for age verification purposes, especially in industries with age restrictions such as gambling or alcohol sales. Accurate age verification is essential to comply with legal requirements and prevent underage access.
Let’s consider an online platform that offers casino games. Before allowing users to access these games, the platform may require them to undergo face liveness verification to verify their age. This helps ensure that only individuals of legal gambling age can participate, promoting responsible gambling practices and adhering to regulatory guidelines.
Benefits for Stakeholders
Face liveness verification offers numerous benefits for various stakeholders involved in online transactions and authentication processes. Let’s explore some of these advantages in more detail:
Merchant Advantages
Merchants stand to gain significantly from integrating face liveness verification into their systems. One key benefit is the reduction of fraud-related losses. By implementing robust face liveness verification technology, merchants can effectively detect and prevent fraudulent activities, safeguarding their businesses from financial harm.
Moreover, face liveness verification enhances customer trust and confidence in online transactions. With the assurance that their identities are being securely verified, customers feel more comfortable engaging in digital commerce. This increased trust translates into higher conversion rates and improved customer satisfaction, ultimately driving business growth.
In addition to these benefits, integrating face liveness verification helps merchants comply with regulatory standards and mitigate legal risks. As data protection regulations become increasingly stringent, organizations must ensure they have adequate measures in place to protect user information. By implementing face liveness verification systems that meet industry standards, merchants demonstrate their commitment to security and minimize the potential for legal repercussions.
Consumer Convenience
For consumers, face liveness verification offers a convenient and hassle-free authentication experience. Gone are the days of struggling to remember complex passwords or carrying around additional hardware devices for two-factor authentication. With face liveness verification, users can securely access services or perform transactions with just their faces.
The simplicity of this authentication method not only saves time but also reduces friction during the login process. Users no longer need to go through multiple steps or wait for codes to be sent to their phones; they can simply look into their device’s camera and gain access instantly.
Trust and Compliance
Face liveness verification plays a crucial role in building trust between organizations and their users. By implementing this technology, organizations demonstrate a commitment to ensuring the security and privacy of user data.
Furthermore, face liveness verification ensures compliance with industry regulations and data protection standards. Organizations that handle sensitive user information must adhere to specific guidelines and safeguard user privacy. Implementing robust face liveness verification systems helps organizations meet these requirements, giving users peace of mind knowing their data is being handled securely.
Technical Aspects of Liveness Solutions
Face liveness verification relies on various technical aspects to ensure accurate and reliable results. Let’s explore some of these key techniques in detail.
Blood Flow Analysis
One crucial technique used in face liveness verification is blood flow analysis. By analyzing the patterns of blood circulation, this method helps differentiate between live human faces and fake representations such as masks or printed photos.
Blood flow analysis adds an additional layer of accuracy to the verification process. It examines the presence of real blood circulation, which is a vital characteristic of a living person. By detecting the unique blood flow patterns in a person’s face, liveness solutions can effectively identify potential fraud attempts.
This technique is particularly useful for high-security applications where it is essential to ensure that only genuine individuals gain access. By incorporating blood flow analysis into face liveness verification systems, organizations can enhance their security measures and protect against impersonation attacks.
Heartbeat Detection
Another important aspect of face liveness verification is heartbeat detection. This technique involves analyzing subtle changes in facial skin color caused by variations in blood flow associated with heartbeats.
Heartbeat detection helps confirm the presence of a live person during the verification process. By monitoring these minute color changes, liveness solutions can determine whether an individual is physically present or if they are using a static image or other non-living representation.
The inclusion of heartbeat detection enhances the reliability and effectiveness of face liveness verification systems, especially in scenarios where stringent security measures are required. It provides an additional layer of assurance by confirming that the individual being verified is indeed alive and actively participating in the process.
Eye Movement Tracking
Eye movement tracking plays a significant role in ensuring accurate face liveness verification. This technique focuses on detecting natural eye blinking or gaze shifts, which are characteristics typically exhibited by live individuals.
By accurately tracking eye movements, liveness solutions can verify that the person being authenticated is physically present and actively engaged. This helps prevent fraudulent attempts using static images or videos.
Eye movement tracking enhances the overall effectiveness of face liveness verification systems by adding an extra layer of security. It ensures that only genuine individuals can pass the verification process, providing organizations with increased confidence in their authentication procedures.
Integrating Liveness Technology
Face liveness verification is a versatile technology that can be seamlessly integrated across various platforms, including mobile devices, web applications, and physical access control systems. Regardless of the platform used for authentication, face liveness verification provides consistent security measures to ensure the integrity of user identities.
Cross-platform compatibility is a key advantage of face liveness verification. It allows users to experience a seamless authentication process across different devices without compromising security. Whether accessing an application on their smartphone or using a desktop computer, users can rely on the same level of protection provided by face liveness technology.
Implementing face liveness verification can also bring cost-efficiency benefits compared to traditional authentication methods. With this technology in place, there is no need for additional hardware investments such as tokens or SMS codes. This eliminates the associated costs and maintenance efforts required for traditional authentication methods. Furthermore, it reduces operational expenses related to password resets and account recovery processes since face liveness verification offers a secure and reliable means of identity verification.
One significant advantage of face liveness verification is its ability to adapt to evolving threats and attack techniques. As new vulnerabilities emerge, face liveness systems continuously update their algorithms and improve their defenses against emerging spoofing methods. This adaptability ensures that the technology remains effective in countering potential threats while maintaining high-security standards.
The continuous updates and improvements made by developers contribute to the effectiveness of face liveness verification systems over time. By staying ahead of potential attacks, these systems provide robust protection against both known and unknown threats.
Accessibility and Regulatory Compliance
Face liveness verification offers numerous benefits. Let’s explore how this technology addresses user accessibility, helps organizations meet compliance standards, and contributes to reducing identity theft.
User Accessibility
One of the key advantages of face liveness verification is its user-friendly nature, particularly for individuals with disabilities. This authentication method eliminates the need for physical interactions or complex actions, making it accessible to a wide range of users. Whether someone has limited mobility or visual impairments, face liveness verification prioritizes user accessibility by providing a seamless and intuitive authentication experience.
By leveraging facial recognition technology, individuals can easily verify their identities by simply looking at the camera. This simplicity ensures that people with different abilities can access services and platforms without facing unnecessary barriers. The design and implementation of face liveness verification systems focus on creating an inclusive environment where everyone can participate securely.
Compliance Standards
In today’s digital landscape, organizations must adhere to various compliance standards related to identity verification and data protection. Face liveness verification plays a crucial role in helping businesses meet these requirements effectively.
For instance, regulations like the General Data Protection Regulation (GDPR), Know Your Customer (KYC) guidelines, or Anti-Money Laundering (AML) laws demand robust identity verification processes. By implementing face liveness verification technology, organizations can ensure compliance with these industry standards.
Complying with such regulations not only enhances trust among users but also builds credibility with regulatory authorities. Face liveness verification provides an additional layer of security that verifies the authenticity of users’ identities while protecting sensitive information from unauthorized access.
Identity Theft Reduction
Identity theft is a significant concern in today’s digital world. Fraudsters constantly seek ways to impersonate others and gain unauthorized access to personal accounts or sensitive data. However, face liveness verification acts as a powerful deterrent against such fraudulent activities.
By relying on advanced algorithms that analyze facial movements and features, face liveness verification makes it extremely difficult for fraudsters to bypass the authentication process. This technology ensures that only genuine users with live and present faces can gain access to protected systems or services.
Conclusion
So there you have it, the ins and outs of face liveness verification. We’ve explored the importance of detecting liveness in facial recognition systems, the various methods used to achieve this, and the benefits it brings to both security and user experience. By integrating liveness technology into their systems, organizations can significantly enhance their security measures while ensuring a seamless and convenient user experience.
Now that you’re armed with this knowledge, it’s time to take action. Whether you’re a business owner looking to bolster your security or a consumer concerned about protecting your personal information, consider implementing or demanding face liveness verification in the systems you use. By doing so, you’ll be contributing to a safer digital environment where your identity is protected from fraudsters and unauthorized access.
So go ahead, embrace the power of face liveness verification and make a difference in the world of cybersecurity. Stay safe out there!
Frequently Asked Questions
What is face liveness verification?
Face liveness verification is a technology that ensures the authenticity of a person’s identity by detecting whether they are a live human or an impersonator. It prevents fraudulent activities such as using photos or videos to bypass facial recognition systems.
How does face liveness verification work?
Face liveness verification works by analyzing various facial features and movements in real-time. It uses advanced algorithms to detect signs of life, such as blinking, head movement, or changes in skin texture. By comparing these cues with pre-determined patterns, it can determine if the person is genuinely present.
Why is liveness detection important for security?
Liveness detection enhances security by preventing spoofing attacks and ensuring that only genuine users gain access. By distinguishing between live individuals and fake representations, it safeguards sensitive information, protects against identity theft, and maintains the integrity of authentication systems.
What are the benefits of implementing face liveness verification?
Implementing face liveness verification brings several benefits. It improves user experience by providing seamless and secure authentication processes. It enhances security measures by preventing unauthorized access attempts and reduces the risk of fraud or identity theft.
Is face liveness technology compliant with regulations?
Yes, face liveness technology can be designed to comply with accessibility standards and regulatory requirements. By incorporating inclusive design principles and adhering to relevant guidelines such as GDPR or CCPA, organizations can ensure that their implementation of this technology respects privacy rights while maintaining security standards.

Add a Comment