Liveness detection is the key to keeping biometric authentication systems secure. This technology ensures that the person providing a biometric sample is indeed alive and not attempting to deceive the system with fake or stolen identities. By implementing active and passive liveness detection techniques, biometric systems can verify the authenticity of users, enhancing both security and accuracy.
In today’s digital landscape, where sensitive information is at risk of unauthorized access, liveness detection plays a critical role in preventing spoofing attacks. It safeguards against presentation attacks by ensuring that only genuine users can access protected data or perform transactions. Without liveness detection, biometric systems would be vulnerable to various forms of manipulation.
With its ability to distinguish between real human presence and fraudulent attempts, liveness detection has become an indispensable component of secure authentication processes.
Biometric Authentication Basics
Authentication technology serves as a crucial layer of defense against presentation attacks and unauthorized access in biometric systems. Face liveness is an important component of this technology, ensuring confidence in the authenticity of the user. These characteristics, known as biometric traits, can include fingerprints, facial features, iris patterns, voiceprints, and more. Authentication technology serves as a crucial layer of defense against presentation attacks and unauthorized access in biometric systems. Face liveness is an important component of this technology, ensuring confidence in the authenticity of the user.
One crucial aspect of biometric authentication is liveness detection. Liveness detection plays a vital role in ensuring the authenticity of biometric samples and preventing presentation attacks. Its primary purpose is to verify that the captured data is from a live person rather than a spoofed representation.
By incorporating liveness detection into biometric systems, they become more resistant to various types of spoofing attempts. Presentation attacks involve presenting fake or stolen biometric data to deceive the system into granting unauthorized access. Liveness detection helps counter such attacks by detecting signs of vitality or presence during the authentication process.
Liveness detection algorithms analyze different aspects of the presented biometric sample to determine its authenticity. For example,These algorithms may assess factors such as eye movement, blinking patterns, head rotation, or response to stimuli like asking the user to smile or nod their head.
Similarly, in fingerprint recognition systems, liveness detection algorithms can analyze blood flow patterns beneath the skin’s surface using techniques like multispectral imaging or analyzing moisture levels on the finger’s surface through capacitive sensors.
The incorporation of liveness detection brings an additional layer of security to biometric authentication systems. By verifying that the presented biometric sample exhibits signs of being from a living person rather than a static image or replica, it significantly reduces vulnerability to spoofing attacks.
Liveness detection has become increasingly important due to advancements in technology and an increased reliance on biometrics for identity verification purposes. As more industries adopt biometric authentication methods in areas such as banking, healthcare records management, access control systems, and mobile devices, the need for robust liveness detection techniques becomes paramount.
Types of Liveness Detection
Liveness detection is a crucial aspect of biometric authentication systems that ensures the authenticity of the user’s identity. There are two main types of liveness detection techniques: passive detection and active detection.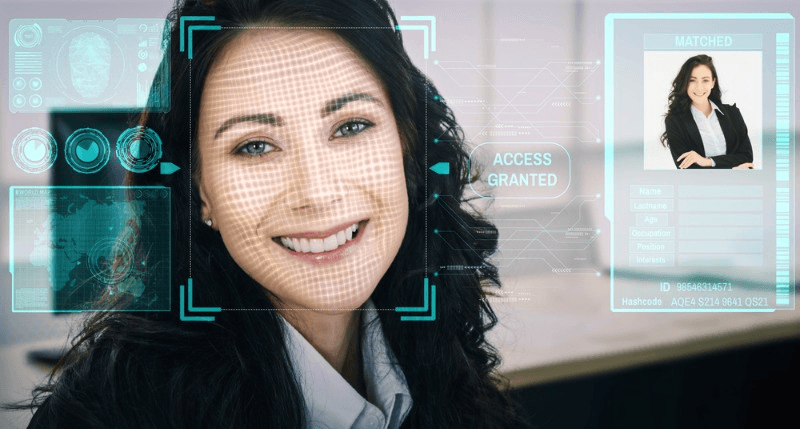
Passive Detection
Passive liveness detection techniques analyze inherent characteristics present in biometric samples without requiring user interaction. Authentication technology serves as a crucial layer of defense against presentation attacks and unauthorized access in biometric systems. Face liveness is an important component of this technology, ensuring confidence in the authenticity of the user.
For example, one passive method involves analyzing the micro-movements of a person’s face using facial recognition technology. By examining subtle changes in facial features like eye movements or slight shifts in skin texture, the system can verify whether the presented image or video is from a live individual.
The advantage of passive detection methods lies in their non-intrusive nature. Users do not need to perform any specific actions during the authentication process, making it seamless and convenient for them. This transparency ensures a smooth user experience while maintaining security measures.
Active Detection
On the other hand, active liveness detection involves user interaction during the authentication process to confirm their liveliness. Authentication technology serves as a crucial layer of defense against presentation attacks and unauthorized access in biometric systems. Face liveness is an important component of this technology, ensuring confidence in the authenticity of the user.
For instance, some systems employ an active technique called “blink detection.” In this method, users are instructed to blink their eyes when prompted by the system. By capturing and analyzing this action in real-time using cameras or sensors, the system can verify that the user is physically present and not attempting to deceive it with static images or videos.
Active detection methods provide an additional layer of security by ensuring the user’s active participation. By requiring specific actions that cannot be replicated by static data alone, these techniques make it significantly more challenging for attackers to bypass biometric authentication systems.
Mechanisms Behind Liveness Detection
Liveness detection is a crucial aspect of biometric authentication systems, ensuring that only live users are granted access. This process involves various mechanisms that help differentiate between genuine users and presentation attacks. Let’s explore some of the key mechanisms behind liveness detection.
Challenge and Response
Challenge and response is a widely used technique in liveness detection. It involves presenting users with random challenges that they must respond to appropriately. By doing so, users demonstrate their ability to interact and follow instructions, which is difficult for static or manipulated images used in presentation attacks.
For example, a challenge may require the user to blink their eyes or turn their head in a specific direction. The system then analyzes the user’s response to determine whether it aligns with the expected behavior for a live person. If the response is accurate, it indicates that the user is genuine.
This mechanism adds an extra layer of security by preventing attackers from using static images or recorded videos to bypass authentication systems.
Depth Perception
Depth perception plays a vital role in liveness detection as it helps identify the spatial relationship between objects within a biometric sample. By analyzing depth information, such as disparities between different parts of the face, systems can detect 3D structures and identify potential spoofing attempts.
For instance, depth perception algorithms can analyze features like facial contours or texture variations on different planes of the face. These analyses enable them to distinguish between real faces and flat surfaces like photographs or masks.
By incorporating depth perception into liveness detection algorithms, biometric systems enhance their accuracy and reliability in detecting presentation attacks.
Motion Analysis
Motion analysis techniques focus on assessing movement within a biometric sample to verify its authenticity. These techniques examine factors such as facial movements, eye blinks, head rotations, or hand gestures to detect signs of vitality.
When a person interacts with an authentication system, they naturally exhibit certain motion patterns that are challenging for attackers to replicate accurately. For example, a live user may blink their eyes, smile, or move their head slightly during the authentication process.
Algorithms and AI in Liveness Detection
Machine learning techniques are at the forefront of developing robust liveness detection algorithms. These algorithms play a significant role in ensuring the authenticity of facial recognition systems. By training models on large datasets containing both genuine and spoofed samples, machine learning algorithms can learn complex patterns and features indicative of liveness.
Through this process, the algorithms become adept at distinguishing between real faces and presentation attacks such as printed photos or videos. The ability to detect these presentation attacks is crucial for preventing unauthorized access to sensitive information and maintaining the security of facial recognition systems.
Artificial intelligence (AI) is also leveraged in various use cases related to liveness detection. AI algorithms excel at analyzing vast amounts of data quickly, enhancing the accuracy and efficiency of liveness detection systems. By processing data rapidly, AI-powered solutions can make real-time decisions about whether a face is live or fake.
Furthermore, AI-based systems continually adapt over time by continuously learning from new data. This adaptability makes them more resilient against evolving presentation attacks that may attempt to deceive the system with increasingly sophisticated methods.
The integration of AI into liveness detection technology has led to significant advancements in its effectiveness. With AI’s ability to analyze patterns and identify anomalies, it becomes easier to differentiate between live faces and fraudulent attempts accurately.
For example, an AI-powered liveness detection system can analyze micro-expressions or subtle movements that are imperceptible to the human eye but indicate a live person. By identifying these unique characteristics, the system can make accurate judgments about the authenticity of a face.
Moreover, AI enables real-time analysis by extracting relevant features from facial images or videos swiftly. This quick analysis allows for immediate decision-making regarding access control or identity verification processes.
Multi-Modality Approach
Liveness detection, a crucial component of biometric authentication systems, often employs a multi-modality approach to enhance its effectiveness and reliability. By combining multiple techniques, these systems can strengthen their security measures and mitigate potential vulnerabilities.
One of the primary advantages of utilizing a multi-modality approach is the ability to leverage different strengths and compensate for weaknesses. Passive and active detection methods work in tandem to provide a comprehensive solution. Passive techniques analyze biometric data without requiring user interaction, while active techniques involve user participation.
By incorporating challenge and response mechanisms, liveness detection systems can verify the authenticity of a user’s biometric data. These mechanisms prompt users to perform specific actions or gestures that are difficult for presentation attacks to replicate accurately. For example, the system may ask users to blink their eyes or smile, ensuring that they are physically present during the authentication process.
Depth perception is another technique commonly used in multi-modal liveness detection. By analyzing depth information captured by 3D cameras or infrared sensors, these systems can determine if an object is flat or three-dimensional. This helps differentiate between real faces and spoofing attempts using printed images or masks.
Motion analysis is yet another powerful tool in liveness detection. By tracking facial movements in real-time, such as blinking or head rotation, the system can identify signs of vitality that cannot be replicated by static images or videos. This dynamic analysis adds an extra layer of security against presentation attacks.
The combination of these techniques significantly enhances the security of biometric authentication systems. Liveness detection ensures that only live users can access sensitive information or perform transactions, reducing the risk of identity theft or fraud. It acts as a robust defense mechanism against various types of presentation attacks, including photo spoofs and video replays.
Organizations that incorporate liveness detection into their authentication processes strengthen their overall security posture and protect user privacy more effectively. Users can have greater confidence in the integrity of the systems they interact with, knowing that their biometric data is being safeguarded against unauthorized access.
Liveness Detection Against Deepfakes
Liveness detection is a crucial tool in the fight against deepfakes, which are manipulated media created using artificial intelligence techniques. These deepfakes can be used to deceive and impersonate individuals by altering their appearance or superimposing their faces onto someone else’s body. However, liveness detection helps identify these fraudulent creations by detecting inconsistencies in facial movements, depth perception, or other vital signs.
Deepfakes have become increasingly sophisticated, making it difficult to distinguish between real and fake content. This is where liveness detection comes into play as an effective countermeasure. By implementing liveness detection technology, organizations can protect themselves against various presentation attacks such as spoofing, replay attacks, or synthetic media manipulation.
One of the primary benefits of liveness detection is that it adds an extra layer of protection during the authentication process. It verifies the presence and vitality of users to ensure that they are physically present and not just a digital representation. This prevents attackers from using pre-recorded videos or images to bypass security measures.
For example, imagine a scenario where an individual attempts to gain access to a secure facility using a deepfake video of an authorized person. Without liveness detection, this impersonation could go undetected and grant unauthorized access. However, with the implementation of liveness detection technology, any inconsistencies in facial movements or vital signs would be detected, alerting security personnel to the attempted fraud.
Liveness detection also plays a critical role in mitigating the risks associated with vulnerabilities in biometric systems. Biometric data such as fingerprints or facial recognition is widely used for authentication purposes. However, these systems can be vulnerable to attacks through forged biometric data or manipulated images.
Features of Effective Verification Systems
Essential Verification Features
Liveness detection is a crucial aspect of biometric verification systems, as it ensures that the biometric sample being used belongs to a live person and not a fraudulent attempt. To achieve this, effective verification systems rely on several essential features.
One such feature is the analysis of facial expressions. By capturing and analyzing the movements of a person’s face, liveness detection algorithms can determine if the individual is displaying natural expressions consistent with a live person. This helps differentiate between genuine users and presentation attacks where static images or videos are used.
Eye movements also play a vital role in liveness detection. The algorithms track the movement of the eyes, including blinking patterns, to verify that the user is actively participating in the authentication process. This dynamic characteristic adds an extra layer of security by ensuring that only live individuals are granted access.
Head rotations are another key factor in liveness detection. By tracking how an individual moves their head during authentication, algorithms can confirm that they are physically present and actively engaged in the process. This prevents impersonation attempts using photographs or videos.
Hand gestures are also utilized for effective liveness detection. Users may be required to perform specific hand movements or gestures during authentication, which cannot be replicated by static images or pre-recorded videos. Analyzing these dynamic characteristics provides further assurance that only genuine users are granted access.
Aware Products Overview
Aware offers a comprehensive range of products and solutions designed to enhance biometrics and liveness detection capabilities within various applications and systems.
Their software development kits (SDKs) enable seamless integration of liveness detection into existing applications or systems. These SDKs provide developers with powerful tools and resources to incorporate Aware’s advanced algorithms and machine learning techniques into their own software solutions.
By leveraging state-of-the-art technologies, Aware products deliver accurate and reliable liveness detection capabilities. Their algorithms have been carefully developed and trained using vast amounts of data, ensuring high levels of accuracy and robustness in differentiating between live individuals and presentation attacks.
One significant advantage of Aware’s products is their adaptability to various biometric modalities. Whether it is facial recognition, iris scanning, or fingerprint authentication, Aware’s solutions can be tailored to meet the specific requirements of different biometric systems. This versatility allows organizations to enhance security across multiple applications and improve overall user experience.
In addition to their powerful liveness detection capabilities, Aware also provides comprehensive support and maintenance services for their products. This ensures that organizations can rely on continuous updates, bug fixes, and technical assistance to maintain optimal performance and security.
With Aware’s range of products and solutions, businesses can enhance the effectiveness of their verification systems by incorporating advanced liveness detection techniques. By leveraging dynamic characteristics such as facial expressions, eye movements, head rotations, hand gestures, and other essential features, organizations can significantly reduce the risk of fraudulent attempts while providing a seamless user experience.
Techniques for Detecting Face Liveness
Facial recognition technology has become an integral part of our lives, from unlocking our smartphones to enhancing security measures at airports and other high-security areas. However, it is crucial to ensure that the facial data being captured is from a live person and not a spoofed image or video. This is where liveness detection comes into play.
Liveness detection is a technique used in biometric systems to verify the liveliness of users during the authentication process. By actively detecting and rejecting presentation attacks, organizations can maintain the integrity and reliability of their biometric systems. Let’s explore some techniques for detecting face liveness.
Facial Recognition Technology
Facial recognition technology relies on liveness detection to enhance security measures. It ensures that the facial data being captured is from a live person, preventing spoofing attempts. Liveness detection can be achieved through various methods such as:
Texture Analysis: This method analyzes the texture of the skin to determine if it exhibits natural properties associated with living beings. For example, micro-movements like slight changes in skin color or wrinkles can indicate the presence of a real person.
3D Depth Analysis: By capturing depth information using infrared sensors or structured light scanners, 3D depth analysis can detect if a face has physical depth and contours associated with a real human face.
Eye Blink Detection: One common approach to liveness detection involves analyzing eye movements and detecting blinks. Since blinking is an involuntary action, it helps distinguish between live subjects and static images.
By combining facial recognition with these liveness detection techniques, organizations can achieve robust and trustworthy authentication systems that are resistant to presentation attacks.
Preventing Presentation Attacks
Presentation attacks refer to attempts made by individuals to deceive biometric systems using fake or manipulated biometric samples such as photos, videos, or masks. Liveness detection acts as a deterrent against such attacks by verifying the liveliness of users during the authentication process.
Some common liveness detection techniques used to prevent presentation attacks include:
Motion Analysis: This technique involves analyzing the motion patterns of a user’s face during the authentication process. It can detect unnatural movements or lack thereof, indicating the presence of a presentation attack.
Thermal Imaging: Thermal imaging cameras can capture and analyze heat patterns on a person’s face. As live human faces emit heat, this technology can distinguish between real faces and masks or other fake representations.
Heartbeat Detection: Heartbeat detection measures subtle changes in blood flow under the skin caused by a person’s heartbeat. By using specialized sensors, it is possible to verify if a user is alive based on their unique cardiac rhythm.
Conclusion on Liveness Detection
Liveness detection is an essential aspect of biometric authentication systems, ensuring the security and authenticity of user identification. By combining passive and active techniques, such as challenge and response, depth perception, and motion analysis, liveness detection provides a comprehensive approach to verify user liveliness.
One key takeaway is that liveness detection plays a crucial role in preventing presentation attacks. These attacks involve using fake or stolen biometric samples to deceive the authentication system. By incorporating advanced algorithms and technologies, liveness detection can detect signs of life that cannot be replicated by static images or recordings.
Another important point is the significant role of machine learning and artificial intelligence in developing robust liveness detection algorithms. These technologies enable the system to learn from a vast amount of data and adapt to evolving threats. As machine learning algorithms become more sophisticated, they can better distinguish between live users and presentation attacks, enhancing the overall security of authentication systems.
Looking into the future, continuous advancements in liveness detection technologies will shape the landscape of authentication security. With presentation attacks becoming more sophisticated, innovative solutions are required to counter emerging threats effectively. Ongoing research and development efforts aim to improve the accuracy, efficiency, and usability of liveness detection for secure authentication.
By leveraging cutting-edge technologies like computer vision and deep learning, researchers are exploring new approaches to enhance liveness detection. For example, depth perception techniques use infrared sensors to capture three-dimensional information about the face, making it harder for attackers to create realistic fake images. Motion analysis algorithms analyze facial movements in real-time, ensuring that only live users can access sensitive information or perform transactions securely.
In conclusion, liveness detection is a crucial component of biometric authentication systems. Its ability to verify user liveliness through a combination of passive and active techniques makes it an effective defense against presentation attacks. Continuous advancements in machine learning, artificial intelligence, and other technologies will shape the future of authentication security, enabling more robust and reliable liveness detection solutions.
Frequently Asked Questions
FAQ
How does liveness detection work?
Liveness detection works by analyzing various factors to determine if a biometric sample, such as a face or fingerprint, is from a live person or a spoof attempt. It uses techniques like facial movements, blinking, blood flow analysis, and depth perception to differentiate between real and fake samples.
Can liveness detection protect against deepfakes?
Yes, liveness detection can help protect against deepfakes. By analyzing subtle facial movements and physiological indicators like pulse or skin texture changes, it can detect the presence of a real person and distinguish them from manipulated or synthetic media.
What are the mechanisms behind liveness detection?
Liveness detection employs different mechanisms to verify the authenticity of biometric samples. These mechanisms include analyzing dynamic features like eye blinking or head movement, utilizing infrared sensors for blood flow analysis, assessing 3D depth information using structured light or stereo cameras, and examining texture consistency on the skin’s surface.
How do algorithms and AI contribute to liveness detection?
Algorithms and AI play a crucial role in liveness detection. They enable the analysis of complex patterns in biometric data by leveraging machine learning techniques. By training on large datasets containing both genuine and fake samples, these algorithms can learn to identify unique characteristics that indicate whether a sample is from a live person or not.
Why is multi-modality approach important in liveness detection?
A multi-modality approach enhances the effectiveness of liveness detection systems. By combining multiple biometric modalities such as face recognition with voice authentication or fingerprint scanning, it becomes more challenging for fraudsters to bypass security measures. This approach adds an extra layer of protection by requiring proof of liveliness across different biometric traits.

Add a Comment